Social media has completely changed how individuals exchange information, communicate, and do business. With billions of members worldwide, social media sites like Facebook, Instagram, LinkedIn, and X have developed into effective resources for networking, marketing, and information exchange.
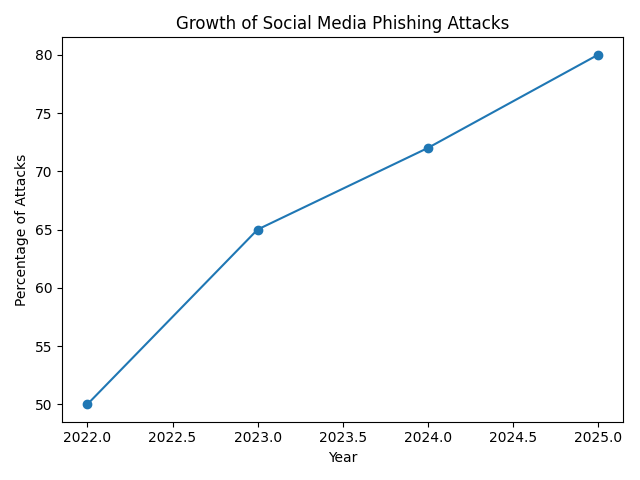
But social media’s explosive expansion has also brought up new cybersecurity issues. These platforms are increasingly being used by cybercriminals to launch phishing attacks, disseminate malware, steal personal information, and pose as businesses.
Businesses, governments, and individuals all need to understand that social media is a possible cybersecurity risk in addition to being a communication route.
In order to safeguard digital identities and organizational data, this article examines how social media contributes to cybersecurity dangers and offers practical mitigation techniques.
The Growth of Cybersecurity Risks and Social Media
The use of social media has increased dramatically during the last ten years. Nowadays, billions of people exchange thoughts, places, images, and personal data online.
Cybercriminals find social media to be a useful target due to the abundance of public data.
Attackers target social media for the following main reasons:
- a big worldwide readership
- Publicly accessible personal data
- High levels of user confidence
- Inadequate password protection
- Quick exchange of information
Social media is a desirable arena for initiating cyberattacks because of these considerations.
Significant Social Media Cybersecurity Risks
Organizations and individuals can take preventive action by becoming aware of the most prevalent social media cyberthreats.
1. Phishing Attacks
One of the most prevalent cybersecurity risks on social media is phishing. Attackers send phony messages or links intended to fool users into disclosing private information.
Examples include statements asserting:
- Requests for account verification
- Winnings from prizes
- Security notifications
- Users may be sent to phony websites that steal login information after clicking the link.
2. Fake accounts and impersonation
Cybercriminals impersonate real people or organizations by creating fictitious profiles.
These accounts could be impersonators of:
- Executives of the company
- Customer service representatives
- Friends or coworkers
- Building confidence with victims and persuading them to provide private information or send money are the objectives.
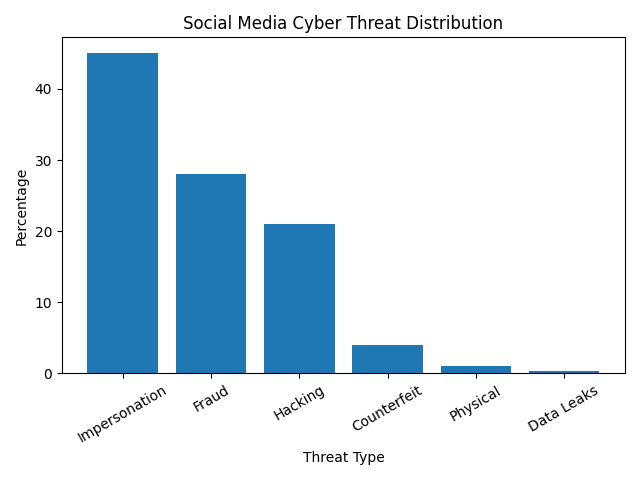
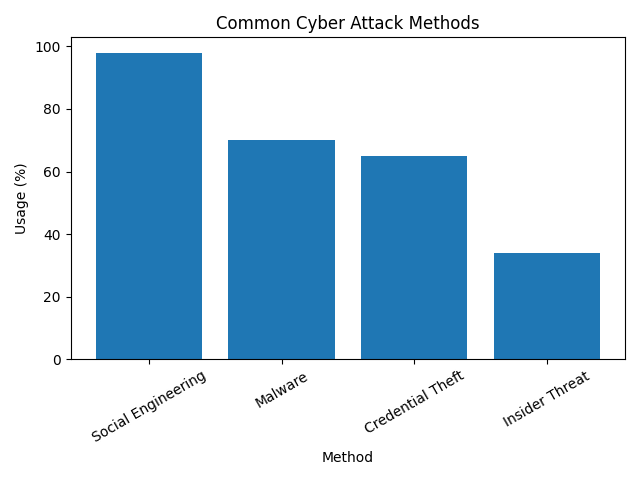
3. Distribution of Malware
When people download infected files or click on dangerous links on social media, malware attacks take place.
Malware is frequently concealed by cybercriminals as:
- Videos that become viral
- Popular news items
- Downloads of free software
- Malware can monitor behavior, encrypt files for ransom, and steal passwords once it has been installed.
4. Attacks Using Social Engineering
Instead of taking advantage of technological flaws, social engineering assaults affect users psychologically.
Attackers could:
- Create fictitious connections
- Develop trust through dialogue
- Request private information
- Because they take advantage of human behavior rather than technology flaws, these attacks are incredibly successful.
5. Cyberattacks Driven by AI
Cybercrime is using artificial intelligence more and more.
Examples consist of:
- Deepfake videos that mimic executives
- Phishing emails produced by AI
- Scams involving voice cloning
- Cyberattacks are more convincing and challenging to identify thanks to these technologies.
Cybersecurity Incidents in the Real World: Insights from the Digital Frontlines
Social media has evolved from a communication tool to a battlefield for cybersecurity threats in today’s hyper connected society. Every cyberattack or data breach has a backstory that shows how vulnerable even the biggest platforms may be. These actual events serve as potent reminders of the importance of taking cybersecurity seriously.
Facebook Data Exposure: When Individual Information Was Made Public
Imagine waking up one day to find that your location, phone number, and profile information were no longer private. When a significant Facebook data hack revealed private user information online, this became a reality for more than 500 million people.
This incident made it very evident how millions of lives can be affected by a single vulnerability.
The LinkedIn Data Scraping Event: Public Information, Private Repercussions
Although many people believe that information that is accessible to the public is safe, the LinkedIn data scraping event revealed a completely different picture. In this instance, information from almost 700 million user profiles was gathered and shared on hacker forums. Despite the fact that the data was theoretically public, its combination gave attackers a potent tool.
This information was exploited by attackers to create highly customized schemes, which greatly increased the convincingness of phishing attempts. Details intended for professional networking, such as job titles, work histories, and relationships, were transformed into tools for deceit. An crucial lesson was brought to light by this incident: even data that is published publicly can be harmful if it ends up in the wrong hands.
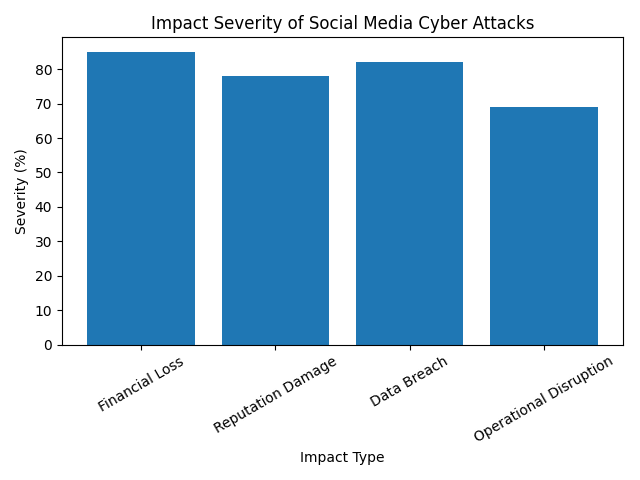
The Effects of Cyberthreats on Social Media
These occurrences are not unique; rather, they are part of an expanding pattern of cyberthreats that impact both people and businesses. The repercussions frequently result in long term harm and go well beyond brief inconvenience.
Loss of Money: The Unspoken Price of Cyberattacks
A cyberattack represents a financial disaster for firms, not merely a technological one. Fraud, ransomware payments, and operational disruptions can cost businesses millions of dollars. Individuals may also experience unapproved transactions or direct money theft. A straightforward phishing message can swiftly turn into an expensive catastrophe.
Reputation Damage: It’s Difficult to Regain Trust Once Lost
Reputation is crucial in the digital world. Years of client confidence can be destroyed by a single hacked social media account. Regaining a brand’s confidence becomes difficult when consumers perceive it to be connected to fraud or data breaches. For many firms, the immediate financial loss is not nearly as serious as the reputational harm.
Data Breach: Sensitive Information Exposure
Cyberattacks frequently result in the disclosure of extremely sensitive data, including as financial information, customer records, and internal conversations. This data can be sold, repurposed, or exploited again once it has been exposed, making recovery incredibly challenging.
Operational Disruption: When Systems Stop Working
Cyberattacks have the potential to interrupt entire enterprises in addition to causing financial and reputational harm. System failures, service outages, or delays can have an impact on businesses’ customer satisfaction and productivity. Such interruptions can have even more dire repercussions in essential businesses.
Cybersecurity Mitigation Techniques: Establishing a Robust Defense
Even if the risks are substantial, they can be avoided. Organizations can lessen their vulnerability to social media cyberthreats and safeguard themselves with the appropriate tactics.
Using Multi Factor Authentication (MFA) to Strengthen Access
Multi factor authentication is one of the best methods for account security. MFA requires further verification, such as a one time code or biometric confirmation, in addition to a password. Even in the event that login credentials are hacked, this additional layer of security makes it far more difficult for attackers to obtain illegal access.
Encouraging Workers with Cybersecurity Education
Cyberattacks cannot be stopped by technology alone; humans are essential. Human error, such as clicking on a malicious link or replying to a bogus message, is the reason why many assaults are successful. Organizations can establish a robust first line of defense by teaching staff members how to spot phishing attempts and suspicious activity.
Controlling Privacy Preferences to Improve Security
Controlling what you share is crucial in a society when sharing has become commonplace. Users are accountable for controlling their privacy settings and limiting the disclosure of private data. Risk can be greatly decreased by taking easy precautions including limiting profile visibility, eliminating location sharing, and concealing phone numbers.
Making Use of Security Monitoring Tools
Proactive monitoring is necessary for modern cybersecurity. Companies should spend money on solutions that monitor social media activity continuously and identify odd activities. Early identification can stop a little problem from becoming a significant breach, whether it’s an illegal login attempt or a dubious link.
Performing Frequent Security Audits
Cybersecurity needs constant assessment; it is not a one time endeavor. Organizations can examine access restrictions, find vulnerabilities, and make sure data protection safeguards are current by conducting regular audits. Businesses can improve their overall security posture by anticipating possible threats.
Upcoming Developments in Social Media Cybersecurity
Cybercriminals’ strategies change along with technology. Both new attacks and sophisticated defenses will influence social media cybersecurity in the future.
AI Powered Attacks: Faster and Wiser Dangers
Attackers are able to automate and expand their activities thanks to artificial intelligence. AI is increasing the effectiveness and difficulty of assaults by creating convincing phishing messages and studying user behavior.
Deepfake Fraud: When It’s Time to Stop Believing
A new degree of deceit is being introduced by deepfake technology. These days, cybercriminals can produce lifelike audio and video recordings that mimic reputable people. This raises the possibility of success and makes schemes seem more plausible.
Disinformation Driven by Bots: Changing Public Perception
The use of automated bots to disseminate false information and sway online conversations is growing. These efforts have the potential to seriously harm people’s reputations, deceive audiences, and cause widespread misunderstanding.
Advanced Threat Identification: Intelligent Defense’s Ascent
Organizations are implementing AI powered defense technologies to quickly identify and address risks. These tools provide hope in the ongoing fight against cybercrime by analyzing patterns, spotting anomalies, and thwarting attacks before they do any harm.
Conclusion: Maintaining Security in an Interconnected World
Social media has become an essential component of contemporary life, providing a plethora of chances for growth and contact. But there are also serious cybersecurity concerns associated with it, as Facebook and LinkedIn’s experiences show.
Cybercriminals are always coming up with new ways to take advantage of users, from phishing schemes to AI driven attacks. Being aware, being ready, and taking proactive measures are the keys to remaining safe. Individuals and companies can defend themselves against changing threats by putting in place robust security measures like multi factor authentication, personnel training, and ongoing monitoring.
Ultimately, cybersecurity is about accountability rather than merely technology. Being knowledgeable, watchful, and one step ahead of cyber threats is essential to remaining safe in an interconnected society.

